Australian Real Estate Cyberattack Claimed by Radar Threat Actor
Read Time 5 mins | 30 October 2025

Australian Real Estate Cyberattack Claimed by Radar Threat Actor
This is an ongoing investigation. This article will be updated as more information becomes available.
Last updated: 20 November 2025
The Australian real estate industry was potentially targeted by a cyberattack claimed by the threat actor "Radar" in October 2025. The actor claimed to have compromised three real estate companies and threatened to release stolen data. However, significant inconsistencies in the evidence, coupled with a missed publication deadline and the subsequent removal of listings, suggest the incident may have been fabricated or has been resolved through undisclosed means.
Key Timeline
- 17 October 2025 – Threat actor claims breach occurred; listings appear on dark web leak sites
- 13 November 2025 – Scheduled data release date passes without publication; deadline extended to 20 December 2025
- 20 November 2025 – All listings removed from threat actor's leak site
17 October 2025: Initial Breach Claims
The Incident
On 17 October 2025, the threat actor "Radar" published listings on dark web leak sites claiming to have compromised multiple entities within the Australian real estate sector. According to the threat actor, the breach occurred on this same date, with a deadline of 13 November 2025 set for data publication if ransom demands were not met.
The Claims
The threat actor claimed to have compromised:
- Sold Real Estate
- One Agency Eastlakes
- UrbanX
- 4 conveyancing firms (names not disclosed)
- 2 law firms (names not disclosed)
- Passport information
Identified Inconsistencies
Rivanorth's analysis identified significant red flags in the threat actor's claims. Much of the information provided regarding One Agency Eastlakes and UrbanX appeared to be duplicated, which raised serious questions about the legitimacy of the breach. The duplication of data samples suggested the attacker's claims might not be genuine.
Supply Chain Implications
What made this incident particularly noteworthy was the potential supply chain impact. Even if the primary real estate companies were not directly breached, the involvement of conveyancers, law firms, and passport data suggested that downstream partners and service providers may have been compromised instead.
This represents a recurring theme in modern cybersecurity: organisations can maintain robust security postures, yet still have their data exposed through third-party vendors and partners. The interconnected nature of the real estate transaction process, which involves multiple parties handling sensitive personal and financial information, creates numerous potential points of failure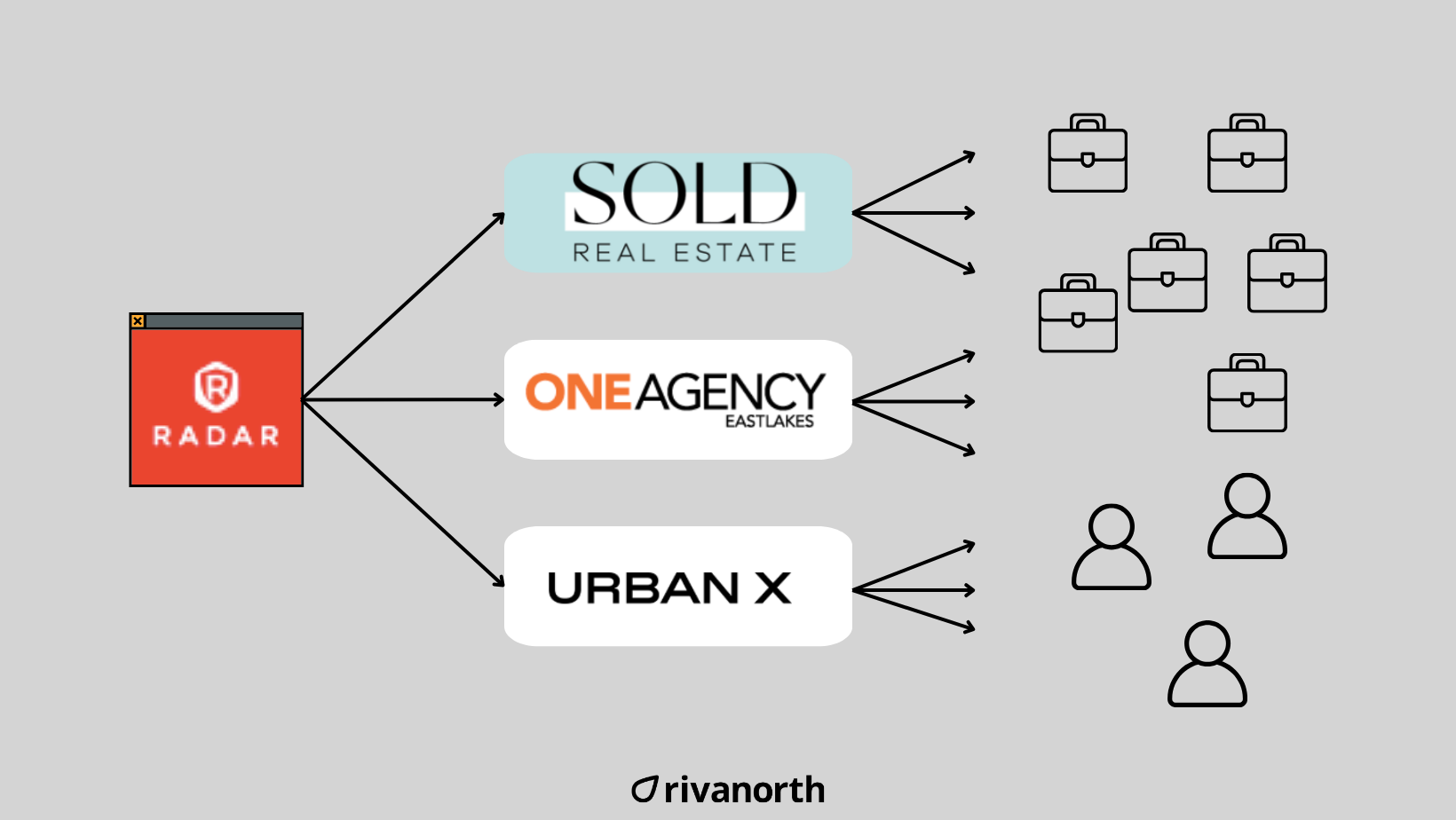
Three Possible Outcomes
Based on the available evidence at the time, there were three potential scenarios:
-
Complete Fabrication – The attacker's claims were entirely false, and no legitimate data breach had occurred. The duplicate information and lack of substantial proof supported this possibility.
-
Significant Industry Breach – The claims were genuine, and the sector was dealing with a sizeable compromise affecting multiple entities in the Australian real estate industry.
-
Extensive Supply Chain Breach – The situation was worse than initially claimed, with additional third parties exposed through compromised service providers, creating a cascading effect throughout the industry.
13 November 2025: Scheduled Release Date Passes
No Data Publication
The originally scheduled data release date of 13 November 2025 passed without any publication of the claimed dataset. All three affected companies subsequently showed a revised deadline of 20 December 2025 on the threat actor's leak site.
Analysis of the Extension
The reason for this extension remained unknown at the time. Several possibilities existed:
- Ongoing ransom negotiations – The extension could indicate active discussions between the threat actor and the affected parties
- Technical difficulties – The attacker may have encountered issues on their end
- Further evidence of fabrication – The extension could support the theory that the claims were not legitimate
The extended deadline provided additional time for affected organisations to conduct thorough security assessments and for the industry to prepare for potential data exposure, should the claims prove legitimate. However, the combination of duplicated data samples and the deadline extension continued to warrant scepticism about the legitimacy of these claims.
20 November 2025: Listings Removed
Disappearance from Leak Site
On 20 November 2025, all listings for the claimed Australian real estate breach disappeared from the threat actor's leak site. This development significantly changed the nature of the investigation and raised new questions about what actually occurred.
Most Likely Scenarios
Based on typical ransomware actor behaviour, the removal of listings most commonly indicates one of the following:
-
Ransom Payment – This is the most common reason for listing removal. If a payment agreement was reached, threat actors typically remove the listing as part of the deal. This would also explain the earlier deadline extension, which may have provided time for negotiation.
-
Fabricated Claims Abandoned – If the breach was indeed fabricated or overstated (as the analysis of duplicate data suggested), the threat actor may have removed the listings to avoid further scrutiny or loss of credibility within the criminal ecosystem.
-
Private Sale Completed – The data may have been sold privately to another party, making public release unnecessary. This sometimes occurs when buyers approach threat actors directly outside of the public leak site marketplace.
Less Likely But Possible Scenarios
While less probable, other explanations could include:
-
Law Enforcement Action – Though this would typically affect the entire leak site rather than specific listings, targeted law enforcement intervention remains a possibility.
-
Internal Dispute – Ransomware groups sometimes experience internal conflicts that lead to listing removals, particularly regarding profit-sharing or operational decisions.
-
Technical Issue – A temporary removal due to technical problems, though this would be unusual for multiple listings disappearing simultaneously.
What This Suggests
The removal of the listings, combined with the earlier evidence of duplicate data and the extended deadline, provides additional context for understanding this incident. If a ransom payment was made, the affected companies would typically not confirm this publicly due to both security considerations and the potential for encouraging future attacks. If the claims were fabricated, the threat actor "Radar" may face credibility issues for future operations within the criminal ecosystem.
Conclusions
What We Know
- The threat actor "Radar" claimed a breach of three Australian real estate companies on 17 October 2025
- Significant inconsistencies were identified in the claimed evidence, including duplicate data
- The initial deadline of 13 November 2025 passed without data publication
- The deadline was extended to 20 December 2025
- All listings were removed from the leak site on 20 November 2025
What Remains Unknown
- Whether any legitimate breach actually occurred
- If a ransom payment was made
- Whether the claims were entirely fabricated
- The full extent of any potential supply chain impact
Supply Chain Impact Analysis
All third-party security implications will be available in Rivanorth Oko. Should any data emerge in the future, comprehensive third-party impact analysis will be available, helping organisations understand their supply chain exposure immediately.
The interconnected nature of the real estate transaction process means that even if the primary companies maintained strong security controls, the involvement of multiple service providers in property transactions creates various potential points of vulnerability that organisations should continue to monitor.
Join Our Newsletter